All modern applications and websites depend heavily on data. Information from diverse sources continuously flows in and out without anyone realizing what’s happening under the hood.
Applications depend upon databases to store and categorize this information. Developers depend upon this functionality and the database’s interface to store and retrieve a wide range of information, including comments on popular videos, scores in multiplayer games, and the products you added to your shopping cart at your favorite online retailer.
This article is your introduction to databases. We’ll cover what is a database, the major types of databases, and the importance of a database management system (DBMS).
Table of content
What are Databases?
A database is any data collection that has been logically modeled.
Technically, you don’t always have to keep a database on a local computer. These days, databases can be hosted and operated from a wide range of systems, including cloud.
In websites and applications, the term “database” is used for a software component that enables users and other components to interact with a data storage system. These components are formally known as database management systems (DBMS) and can be set up on any compatible platform.
Databases have been around since the 1960s. In these years, the underlying technology has progressed far enough to make databases an indispensable software component of any modern business system. In fact, many industries would collapse if you could somehow remove the databases from their processes.
Let’s now discuss the types of databases available in the market today.
Types of Databases
Databases are incredibly versatile; you can find a database type to fit your specific operational requirements.
Here is a short overview of the major types of databases.
1. Relational Databases (RDBMS)
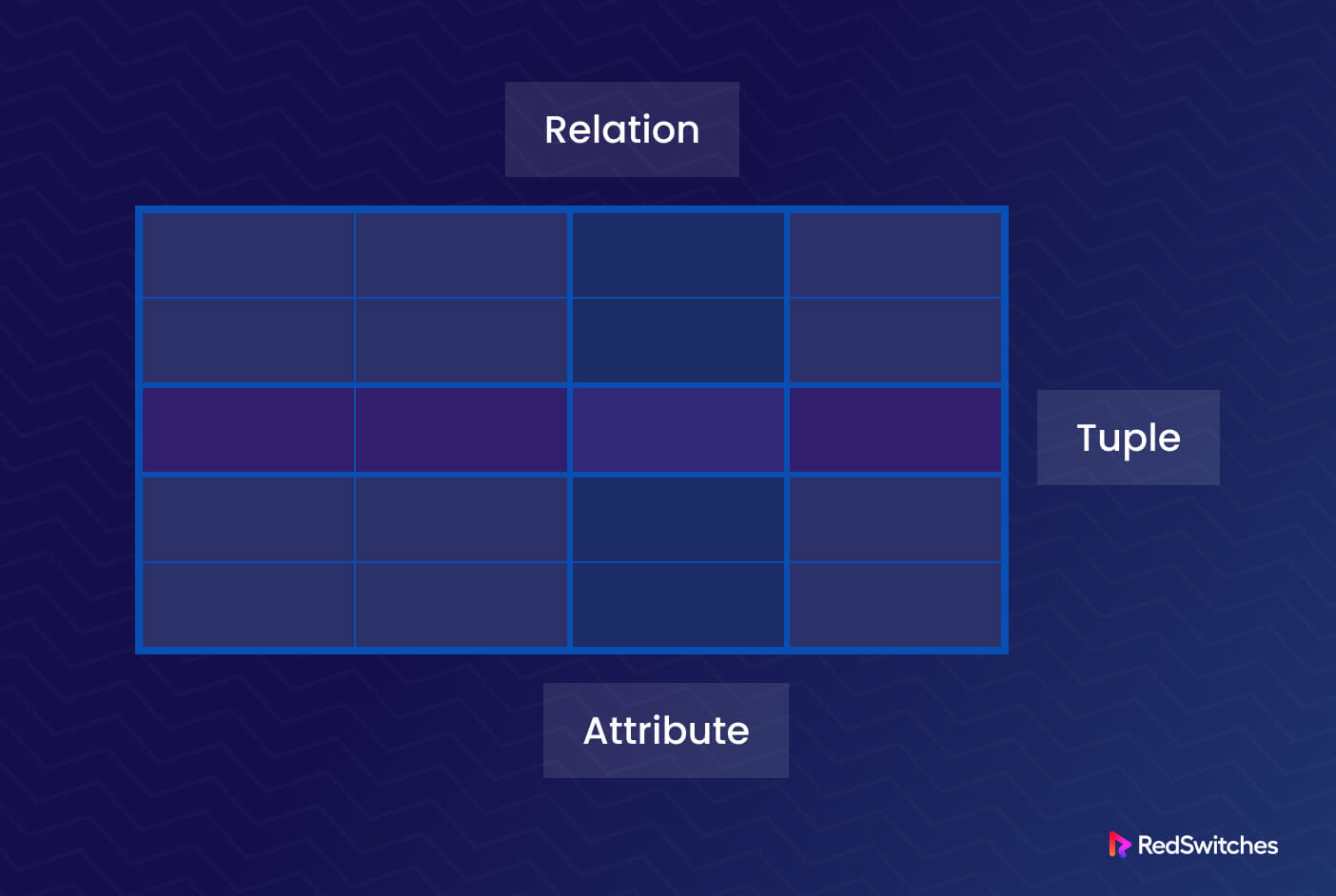
Since the 1970s, the relational model has formed the foundation of most available DBMSs. Relations, which users and modern relational DBMSs (RDBMSs or relational databases) recognize as tables, are the most crucial elements of the relational paradigm. A relation is a collection of tuples, or table rows, each of which shares a set of characteristics or table columns.
Each tuple represents an instance of the database’s items or associations. In the relational model, every table has at least one primary key field that may be used to identify each entry uniquely.
A foreign key is one way to connect two tables. Here, the primary key of one table (the “parent” table) is copied and placed in a column of another table (the “child”) to create a foreign key.
Popular examples include Oracle, MySQL, Microsoft SQL Server, and PostgreSQL.
Key features of Relational databases include:
- Structured data storage with predefined schemas.
- The tables are linked through primary and foreign keys, which define relationships.
- The Structured Query Language (SQL) queries and manipulates data.
- The ACID (Atomicity, Consistency, Isolation, Durability) model ensures data integrity and transaction management.
2. NoSQL Databases
NoSQL (Not Only SQL) databases offer numerous schema choices and are built to handle unstructured or semi-structured data. Prominent examples include MongoDB, Cassandra, Redis, Couchbase, and Neo4j.
Noteworthy characteristics include:
- An absence of rigid schemas allows data storage in diverse formats like key-value, document, columnar, or graph.
- The structure is scalable and can manage large datasets and high-traffic applications.
- The CAP theorem (Consistency, Availability, Partition tolerance) permits trade-offs among these properties without noticeable performance degradation.
- NoSQL databases are designed for distributed environments and horizontal scalability.
3. Object-Oriented Databases (OODBMS)
In OODBMS, data is stored in a design that treats data items as objects. These databases follow object-oriented design principles; thus, developers can apply OOP principles in their code. Examples encompass Versant Object Database, ObjectDB, and Db4o
Key attributes include:
- Objects can encapsulate complex data structures and associated behaviors.
- Support for inheritance, encapsulation, and polymorphism.
- Direct access and manipulation of objects through compatible code.
- Object Query Language (OQL) facilitates data retrieval
4. Hierarchical Databases
In this class of databases, data is arranged in a tree-like form with parent-child connections that determine relationships and hierarchies. Popular implementations include Windows Registry and IBM’s Information Management System (IMS).
Key aspects include:
- Each record has a single parent but can possess multiple children
- Ideal for one-to-many relationships.
- Navigation occurs hierarchically, following parent-child paths.
5. Network Databases
Network databases are similar to hierarchical databases but enable more complex interactions.
Salient characteristics include:
- Records can have multiple parents, forming a network-like structure.
- Navigation relies on record pointers.
- Effective for many-to-many relationships.
6. Time-Series Databases
Time-series databases are optimized for handling data with timestamps and time-based analysis. Noteworthy examples are InfluxDB, Prometheus, and OpenTSDB.
Key features include:
- Efficient time-series data storage and retrieval. Ideal for storing sensor readings, financial data, and log files.
- Specialized indexing and compression techniques catered to time-series data analysis.
- Support for data aggregation and analysis based on time intervals.
7. Non-relational Databases
The majority of apps store and organize data using the relational database model. However, not all applications benefit from this model. For instance, although being excellent for storing structured data, it is challenging to scale relational databases horizontally. In addition, they are less effective at storing unstructured data.
Because of these and other problems of the relational framework, developers often use non-relational databases as alternatives.
These alternative models are called NoSQL databases since they frequently do not require SQL to define or query data. This also implies that many NoSQL databases use a distinct syntax for inserting and accessing data.
“NoSQL” and “non-relational” are broad umbrella terms covering several alternative database types labeled as NoSQL.
8. Key-Value Databases
Key-value stores, commonly referred to as key-value databases, are used to organize and maintain association collections.
A collection of key-value pairings, commonly called a dictionary or hash table, is known as an associative array. The key serves as a specific identifier for retrieving the associated value. Values can vary from simple items like integers or texts to more complicated objects like JSON structures.
The key-value database model differs from other models in that the data in a key-value database is considered opaque, and the database is unaware of or concerned with the data it contains. Instead, it is up to the application to decide what data item is saved where in the database.
Redis is a well-known open-source key-value database.
9. Document-Oriented Databases
NoSQL databases that store data as documents are known as “document-oriented databases” or “document stores.”
.Document stores are a type of key-value store where the value is the actual document, and the key is each document’s unique identifier. Additionally, each document in a document store contains some form of metadata that lends some structure to the data.
Accessing documents based on metadata is commonly provided through an API or query language in document repositories. They also support advanced data structures by allowing you to arrange documents within other documents.
MongoDB is a popular document database that can store documents written in BSON, a binary form of JSON.
10. Columnar Databases
Columnar databases, or column-oriented databases, store data in columns. While this design might look similar to a conventional relational database, each column is saved in its file or area in the system’s storage rather than being grouped into tables.
The first item in one column is connected to the first entry in other columns because a columnar database stores data in record order.
Instead of reading every row in a table and discarding extra data after storing it in memory, this design enables queries to read just the necessary columns.
Cassandra is a popular open-source column store.
These are just a few popular types of databases, and you can find other variations and specialized databases, such as graph and spatial databases. The choice of a database system depends upon factors such as the application’s unique requirements, the data’s nature, scalability requirements, and performance expectations.
Understanding Database Management Systems (DBMS)
Users can construct, manipulate, and administer databases using custom-built software called a database management system (DBMS). A DBMS guarantees effective and safe data storage and retrieval and offers a user interface for database interaction.
Let’s look at some of the critical DBMS features:
Structured Data
DBMS works with organized, structured data. As a result, DBMSs can handle a wide range of data formats, such as text, numbers, photos, and multimedia, with equal ease.
DBMS Architecture
A DBMS’s architecture usually consists of three layers: the View layer (user interface), the Logic layer (schema design and data processing), and the Physical layer (storage management).
Data Models
A data model outlines a database’s logical layout and how the data is arranged. Standard data models include relational, hierarchical, network, and object-oriented models.
The relational database management system (RDBMS) is the most popular model many applications use for data management. It arranges data into tables with columns for characteristics and rows for records. This model uses SQL to manipulate and retrieve data.
A database’s entire structure, including all of its tables, the connections between them, constraints, and permissions, is logically described by its schema. It outlines the database’s data organization and structure.
Users can communicate with databases by delivering requests for data retrieval and manipulation using a query language. SQL is the most widely utilized query language for relational databases.
Data Integrity
DBMS maintains data integrity by enforcing the data constraints and rules specified in the schema. This is critical for preventing data discrepancies and ensures the database only contains legitimate data.
Concurrency Control
The DBMS controls concurrent database access by multiple users and applications. It handles transactions and guarantees data consistency and integrity in a multi-user scenario.
Security
DBMS offers several features to safeguard data against unauthorized access and maintain data privacy. These features set up access control, user authentication, and encryption.
How Databases Function as Part of An Application
A database management system isn’t particularly useful on its own. Although a DBMS may be used to query and interact with a database directly, it is usually utilized in conjunction with other tools in real-world situations since it cannot supply or display content on its own.
However, the features of a DBMS transform a database into a crucial element of a more extensive application. As such, you’ll find a DBMS included in several notable open-source technology stacks.
Here are a couple of examples:
- The LAMP stack: LAMP represents a Linux-based stack comprising the MySQL database, the Apache web server, and PHP for processing dynamic content. LAMP is a flexible stack; you can replace components to fit your project’s requirements. For instance, MySQL is often replaced with PostgreSQL or SQLite, PHP with Flask or Django, and Apache by NGINX. Other L*MP alternatives, such as LEMP (with E for NGINX), are also popular.
- The Elastic Stack: The Elastic stack, formerly known as the ELK Stack, is built on ElasticSearch, a search engine based on a document-oriented database. This is frequently used to store program output logs at scale.
These stacks often use a monolithic architecture where several servers are used to implement individual stack components. This configuration makes linking other stack components to a DBMS relatively easy.
Additionally, you may build a remote database by setting up the DBMS on a different (remote) server. You can connect an application server to your remote database through a dedicated DBMS port. MySQL, for example, has a default port 3306, and Redis has a port 6379. This remote database server allows developers to grow the database independently of the application codebase. This results in a highly scalable alternative to monolithic applications.
On the flip side, setting up a remote database increases the attack surface of your application by exposing additional opportunities for unauthorized access. Additionally, since the data must be sent through a network connection from the database server to the application server, the probability of interception multiplies.
Many DBMSs optionally encrypt data to protect it against sniffing attempts. When enabled, these options convert plaintext (the original information format) into ciphertext (an unintelligible form that can only be read by a person or computer with the necessary keys to decode). So, even when a hacker can intercept encrypted data, they cannot read it until they can decode it.
By setting the DBMS to require Transport Layer Security (TLS), you set up an encrypted connection between your database server and any clients or applications needing access. TLS uses certificate-based authentication to encrypt data as it travels over a network.
However, note that TLS only encrypts data in transit. The static data saved on the database server, sometimes referred to as data at rest, won’t be secured even if you’ve set the DBMS to demand TLS connections.
Working with Databases
The majority of database management systems include a command line utility that allows you to communicate with the database. Examples include the MongoDB Shell, psql for PostgreSQL, and MySQL’s mysql command line client.
You can also use third-party command line clients for several DBMSs. Redli is one such example, which functions as an alternative to Redis’s basic redis-cli tool and includes additional functionality.
However, some users may find it challenging to maintain data using a command line interface, which is why many open-source DBMSs come with graphical database administration tools. Some are browser-based, such as phpMyAdmin or pgAdmin, while others, such as MySQL Workbench or MongoDB Compass, are designed to access a remote database from a local machine.
Conclusion
This article introduced databases and covered topics such as major databases, the importance of DBMSs, and how databases function as software components of applications. Understanding these concepts enables users and developers to work effectively with databases.
Discover RedSwitches’ dedicated hosting for efficient database management. We ensure reliable performance and efficient data storage and retrieval with robust server solutions, including powerful database hosting options. Whether you need a relational database, NoSQL database, or object-oriented database, we have the right hosting solution for your projects. Visit our website today to learn more about optimizing database management with RedSwitches’ dedicated bare-metal hosting.
FAQs
Q. What is the purpose of a database?
A database offers efficient storage and management of large volumes of data. It provides a structured and organized data storage method, simplifying the information retrieval, updating, and analysis process.
Q. What are the different types of databases?
There are various database types, each created for particular use cases. The main types include:
- Relational databases: Organize data into tables with rows and columns linked through relationships.
- NoSQL databases provide high scalability and are appropriate for unstructured and semi-structured data.
- NewSQL databases ensure ACID compliance and scalability by combining the advantages of relational and NoSQL databases.
Q. What is SQL, and why is it important?
Relational databases can be accessed using the robust Structured Query Language (SQL). It is an essential tool for database management because it enables users to carry out a variety of operations, including data querying, updating, and deletion.
Q. How does data modeling contribute to database design?
The process of defining the structure and laws that govern data in a database is known as data modeling. It creates a blueprint of how data elements relate to each other and ensures data integrity and accuracy.
Q. What is data normalization, and why is it necessary?
Data normalization is a method for effectively organizing data in a relational database. It reduces redundancy and improves data integrity by eliminating duplicate information, leading to better database performance.
Q. What are primary keys and foreign keys in a relational database?
- Primary keys: These unique identifiers for each record in a table ensure data uniqueness and serve as a reference point for relationships between tables.
- Foreign keys are attributes that help establish relationships between tables by referencing the primary key of another table.
Q. How do databases contribute to data-driven decision-making?
Databases provide a reliable and centralized data repository and enable businesses to make informed decisions based on real-time and historical data analysis.
Q. What is the role of databases in web applications?
Databases play a vital role in web applications by storing user information, content, and application data. They support dynamic content generation and ensure seamless user experiences.
Q. How do NoSQL databases differ from traditional relational databases?
NoSQL databases are suitable for handling unstructured or rapidly changing data because they lack a schema and use flexible data models. They are horizontally scalable and can handle Big Data applications efficiently.
Q. What are the challenges in database management?
Database management can present challenges such as data security, performance optimization, data backup and recovery, and data consistency across different systems.
Q. What are the best practices for ensuring database security?
Implementing strong access controls, encrypting sensitive data, regularly updating database software, and conducting security audits are some of the best practices to enhance database security.