DDoS Protected Dedicated Server
Get a dedicated server with included DDoS protection for your most critical applications. Protect your hosted websites and web applications from 25+ malicious DDoS attacks.
Choose RedSwitches Because.
Why Choose RedSwitches DDoS Protected Dedicated Servers?
DDoS Detection
DDoS Detection
Detect DDoS attacks the moment they are attempted. With a DDoS protected dedicated server from RedSwitches, DDoS attacks are detected within 0 to 90 seconds.
DDoS Mitigation
DDoS Mitigation
Don't let malicious traffic reach your hosted services. Our DDoS protection software reroutes malicious traffic from your web services and never lets it pass through.
24/7/365 Support
24/7/365 Support
Our team of expert engineers is available around the clock. Get in touch with us to report any issues or questions you may have. We'll resolve them within moments.
Transparent, Fixed & Competitive
Pricing Options
| CPU | CORES | RAM | STORAGE | NETWORK | SETUP | PRICE/MO. | |
|---|---|---|---|---|---|---|---|
| 1xIntel E3-1230 Passmark: 7848 |
4C/8T @3.2 Ghz 8vCores |
16GB DDR4 |
2x1 TB HDD |
1 Gbps 30TB |
12H |
€69.00 | Deploy |
| 1xIntel E-2274G Passmark: 9660 |
4C/8T @4.0Ghz 8vCores |
32 GB DDR4 |
2x480 GB SSD |
1 Gbps 30 TB |
12H |
€99.00 | Deploy |
| 1xIntel E-2286G Passmark: 14384 |
6C/12T @4.0 Ghz 12vCores |
64 GB DDR4 |
2x960 GB SSD |
1 Gbps 30 TB |
12H |
€129.00 | Deploy |
| 2xIntel E5-2620v4 Passmark: 16190 |
16C/32T @2.1Ghz 32vCores |
64 GB DDR4 |
2x480GB SSD |
1 Gbps 30 TB |
12H |
€219.00 | Deploy |
| 1 x AMD EPYC 7302P Passmark: 32480 |
16C/32T @3.0 Ghz 32vCores |
64 GB DDR4 |
2x480 GB SSD |
1 Gbps 30 TB |
12H |
€229.00 | Deploy |
| 2xIntel E5-2630v4 Passmark: 19630 |
20C/40T @2.2 Ghz 40vCores |
128 GB DDR4 |
4x480 GB SSD |
1 Gbps 100TB |
12H |
€249.00 | Deploy |
| 2xIntel E5-2650v4 Passmark: 13079 |
24C/48T @2.2 Ghz 48vCores |
128 GB DDR4 |
2x960GB SSD |
1 Gbps 100TB |
12H |
€379.00 | Deploy |
| 2xIntel Silver 4214 Passmark: 23761 |
24C/48T @2.2 Ghz 48vCores |
256 GB DDR4 |
4x960GB SSD |
1 Gbps 100TB |
72H |
€529.00 | Deploy |
| 2xIntel Gold 5118 Passmark: 35642 |
24C/48T @2.3 Ghz 48vCores |
128 GB DDR4 |
2x480GB SSD |
1 Gbps 100TB |
72H |
€449.00 | Deploy |
| 2xIntel Gold 5218 Passmark: 35642 |
32C/64T @ 2.3 Ghz 64vCores |
256 GB DDR4 |
2x1.92 TB GB SSD |
1 Gbps 100TB |
72H |
€599.00 | Deploy |
| 2xAMD EPYC 7402 Passmark: 58436 |
48C/96T @2.6Ghz 96vCores |
256 GB DDR4 |
4x960 GB SSD |
1 Gbps 100TB |
72H |
€639.00 | Deploy |
- CPU
- 1xIntel E3-1230
- Passmark: 7848
- CORES
- 4C/8T @3.2 Ghz
- 8vCores
- RAM
- 16 GB
- DDR4
- STORAGE
- 2×1 TB
- HDD
- NETWORK
- 1 Gbps
- 30 TB
- SETUP
- 12H
- €69.00
- Per Month
- CPU
- 1xIntel E-2274G
- Passmark: 9660
- CORES
- 4C/8T @4.0 Ghz
- 8vCores
- RAM
- 32 GB
- DDR4
- STORAGE
- 2×480 GB
- SSD
- NETWORK
- 1 Gbps
- 30 TB
- SETUP
- 12H
- €99.00
- Per Month
- CPU
- 1xIntel E-2286G
- Passmark: 14384
- CORES
- 6C/12T @4.0 Ghz
- 12vCores
- RAM
- 64 GB
- DDR4
- STORAGE
- 2×960 GB
- SSD
- NETWORK
- 1 Gbps
- 30 TB
- SETUP
- 12H
- €129.00
- Per Month
- CPU
- 2xIntel E5-2620v4
- Passmark: 16190
- CORES
- 16C/32T @2.1Ghz
- 32vCores
- RAM
- 64 GB
- DDR4
- STORAGE
- 2×480 GB
- SSD
- NETWORK
- 1 Gbps
- 30 TB
- SETUP
- 12H
- €219.00
- Per Month
- CPU
- 1 x AMD EPYC 7302P
- Passmark: 32480
- CORES
- 16C/32T @3.0 Ghz
- 32vCores
- RAM
- 64 GB
- DDR4
- STORAGE
- 2×480 GB
- SSD
- NETWORK
- 1 Gbps
- 30 TB
- SETUP
- 12H
- €229.00
- Per Month
- CPU
- 2xIntel E5-2630v4
- Passmark: 19630
- CORES
- 20C/40T @2.2 Ghz
- 40vCores
- RAM
- 128 GB
- DDR4
- STORAGE
- 4×480 GB
- SSD
- NETWORK
- 1 Gbps
- 100 TB
- SETUP
- 12H
- €249.00
- Per Month
- CPU
- 2xIntel E5-2650v4
- Passmark: 13079
- CORES
- 24C/48T @2.2 Ghz
- 48vCores
- RAM
- 128 GB
- DDR4
- STORAGE
- 2×960 GB
- SSD
- NETWORK
- 1 Gbps
- 100 TB
- SETUP
- 12H
- €379.00
- Per Month
- CPU
- 2xIntel Silver 4214
- Passmark: 23761
- CORES
- 24C/48T @2.2 Ghz
- 48vCores
- RAM
- 256 GB
- DDR4
- STORAGE
- 4×960 GB
- SSD
- NETWORK
- 1 Gbps
- 100 TB
- SETUP
- 72H
- €529.00
- Per Month
- CPU
- 2xIntel Gold 5118
- Passmark: 35642
- CORES
- 24C/48T @2.3 Ghz
- 48vCores
- RAM
- 128 GB
- DDR4
- STORAGE
- 2×480 GB
- SSD
- NETWORK
- 1 Gbps
- 100 TB
- SETUP
- 72H
- €449.00
- Per Month
- CPU
- 2xIntel Gold 5218
- Passmark: 35642
- CORES
- 32C/64T @ 2.3 Ghz
- 64vCores
- RAM
- 256 GB
- DDR4
- STORAGE
- 2×1.92 TB GB
- SSD
- NETWORK
- 1 Gbps
- 100 TB
- SETUP
- 72H
- €599.00
- Per Month
- CPU
- 2xAMD EPYC 7402
- Passmark: 58436
- CORES
- 48C/96T @2.6Ghz
- 96vCores
- RAM
- 256 GB
- DDR4
- STORAGE
- 4×960 GB
- SSD
- NETWORK
- 1 Gbps
- 100 TB
- SETUP
- 72H
- €639.00
- Per Month
You Name it & We Will Arrange It
Custom Server Request
Omni-Channel Support
Support Across Tickets,
Emails & IM's
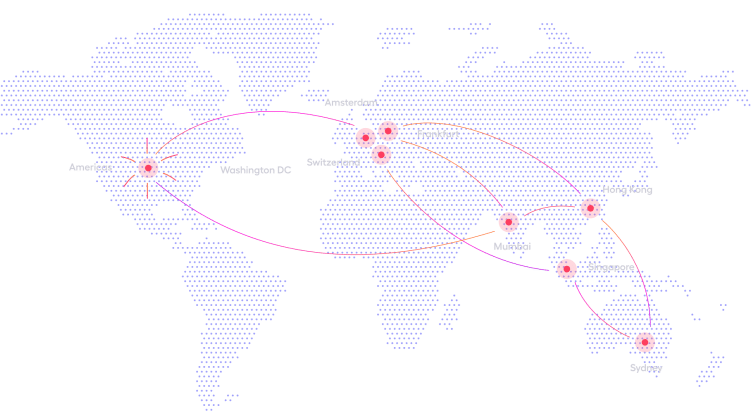
Develop Locally, Deploy Globally
DDoS Protected Dedicated Servers Anywhere in the World
We have powerful dedicated servers with included DDoS protection in data centers
around the globe. Pick a location closest to your users
and enjoy latency-free hosting.

Our Clients & Partners














Happy Clients
TrustScore 4.3 - Excellent Trustpilot
DDoS Protected Servers FAQ
A distributed denial of service (DDoS) attack sends malicious traffic to your server that looks like regular traffic and crashes your hosted web service by overwhelming your server.
DDoS attacks can take your website or web app out of service for days or months, until you stop the incoming harmful traffic. While your website is down, you will likely lose profit and valuable customers.
An easy way to protect your hosted services from DDoS attacks is to get a DDoS protected dedicated server.
- Attack from your competition. There is always a chance that your competition sends a DDoS attack your way if your business is doing well.
- Getting a ransom. Hackers frequently use DDoS attacks to get a ransom. They wouldn‘t stop the DDoS attack until you pay them a certain amount of money they request.
- Simply for fun. Hackers might simply want to have fun with DDoS attacks. They would find a website that is unprotected and send a DDoS attack towards it to entertain themselves.
When a DDoS attack comes your way, the dedicated server identifies the traffic as malicious and reroutes it from your hosted services.
Then, it analyzes the traffic and doesn‘t let it pass through to your website if it is harmful. If it was a false positive, the traffic is allowed to pass through.
RedSwitches offers free DDoS protection with all dedicated server packages that protects your server from all known DDos attacks, such as:
- Application layer attacks: HTTP floods, GET and POST attacks, slowloris, low and slow attacks, and other attacks that target Apache or Windows vulnerabilities.
- Volumetric based attacks such as UDP, ICMP, and different spoofed-packet floods.
- Protocol attacks, including fragmented packet attacks, Ping of Death, SYN floods, Smurf DDoS, etc.
- E-Commerce sites
- Education platforms
- Staging servers
- Email servers
- Online banking software
- SaaS applications
- Customer portals
- Gaming servers
- and more.
The easiest way to protect your website or web application from DDoS attacks is by getting a dedicated server with built-in DDoS protection.
All RedSwitches dedicated server packages come with free 5Gbps DDoS protection.
Not sure exactly what you need?
No problem! Our talented engineers are here to help!
We will consult, architect, migrate, manage and do whatever it takes to help your business grow and succeed.