Imagine you’re having a nice weekend browsing the internet when your computer’s performance suddenly drops. You notice your fan working overtime and everything moving slower. Unknown to you, your computer has been compromised by cryptojacking. This cyber security issue involves hackers hijacking your device resources to mine cryptocurrencies.
Cybercriminals profit by exploiting your device’s processing power without your permission, leaving you with a sluggish and vulnerable system. This growing digital threat emphasizes the significance of cybersecurity measures to protect against unauthorized system access and resource exploitation.
In this article, we will examine two questions: what is cryptojacking, and how can you protect your devices from it?
First, let’s start with the definitions.
Table Of Contents
- What Is Cryptojacking?
- How Cryptojacking Works
- Detecting and Preventing Cryptojacking
- Conclusion
- FAQs
What Is Cryptojacking?
Cryptojacking (malicious crypto mining) is an online threat that hides on user devices and exploits the machine’s resources to “mine” cryptocurrencies.
Malicious crypto miners are frequently distributed via web browser downloads or compromised mobile apps. Cryptojacking can infiltrate many devices, including desktops, laptops, cell phones, and network servers.
Like all online threats, the objective is profit. However, unlike many threats, cryptojacking attacks are meant to continue for a long time while remaining hidden from the user. That’s why cryptojacking is carried out through sophisticated tactics and a well-written codebase.
After this introduction, let’s look into the mechanics of this threat.
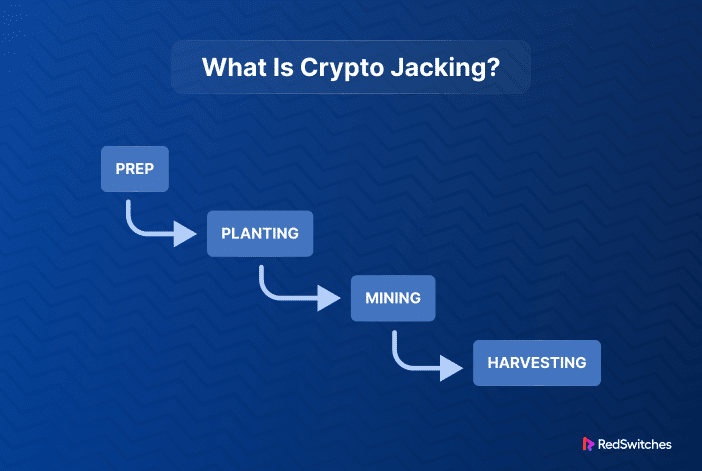
How Cryptojacking Works
Every cryptojacking attack is different because of the way the attack is initiated and how the mining operations work.
Here’s a look at a typical cryptojacking attack.
Step No 1: Infiltration and Infection
Cybercriminals compromise devices to install cryptojacking software. The software is delivered via suspicious download archives and compromised apps. Once activated, the software starts mining in the background and attempts to steal from cryptocurrency wallets. The unwitting victims continue using their gadgets typically, with some noticing the sluggish performance or lags.
Hackers have several methods for launching these attacks:
- Tricking the user to click on a malicious link in an email or website. The crypto mining code is loaded on the victim’s computer, responding to the user’s action.
- Infect a website or online advertisement with JavaScript code that executes automatically once loaded in the victim’s browser.
Step No 2: Resource Utilization
The initialization code installs a cryptojacking script on the victim’s device and sets it to run in the background while the victim uses it. Regardless of the approach employed, the script executes complicated mathematical problems on the compromised devices and sends the outputs to a server controlled by the hacker.
Cryptojacking scripts, unlike other varieties of malware, do not harm computers or victims’ data. They do, however, steal computer processing resources. Users might be irritated by the decreased device performance but usually don’t take any action because there is no imminent danger to the data or device. Cryptojacking is problematic for businesses since organizations with multiple cryptojacked systems pay high costs regarding wasted resources and increased power consumption.
Step No 3: Communication With the Command and Control Server
Cryptojacking software communicates with the attacker’s command and control (C&C) server. This communication channel is the principal mechanism for the attacker to control and manage the infected devices remotely. The C&C server is a centralized hub from which the attacker may send malware instructions and receive updates or information about infected systems.
This connection is frequently made through various means, such as domains, IP addresses, or even decentralized networks.
The Mining Process of Cryptojacking Malware
In cryptojacking, the mining process entails utilizing the processing resources of infected devices to solve complex mathematical problems. These issues are critical to validating transactions and adding new blocks to the blockchain, which is the foundation for most cryptocurrencies.
When an infected device begins mining, it joins a network of miners vying to solve these mathematical puzzles. The first miner who solves the challenge is rewarded with newly minted cryptocurrency coins or tokens and gets to add the next section of transactions to the blockchain.
This payment is intended to encourage miners to contribute computer power to the blockchain network’s integrity.
Malware Stealth and Concealment
Cryptojacking malware utilizes various techniques to avoid detection and continue to mine without the user’s knowledge. Some strategies are:
Low Resource Consumption: Cryptojacking malware is designed to consume as few CPU and memory resources as possible, ensuring that the infected device’s performance decline is mild and does not raise suspicion.
Randomization: The malware may use domain generation algorithms (DGAs) techniques to communicate with the C&C server. This makes blocking communication based on static domain lists more difficult for security solutions.
Encryption: Communication between the malware and the C&C server is frequently encrypted to prevent interception and analysis of the instructions.
Detecting and Preventing Cryptojacking
After answering what is cryptojacking, the next critical challenge is to discuss in detail the detection and preventive measures of cryptojacking.
How to Identify the Signs of Cryptojacking
Cryptojacking detection can be challenging because the malware and its mining process are well hidden or disguised as benign activity on the compromised device. However, there are some warning signs to look out for:
Reduced Performance
One of the primary signs of cryptojacking is a drop in the device performance. Systems that slow down without significant workload changes should be inspected for cryptojacking malware. In worse cases, the system starts crashing or performing exceptionally poorly. A related symptom is the rapid depletion of the device battery.
Device Overheating
Because cryptojacking is a resource-intensive activity, computing systems start overheating. This can damage the system and severely limit their lives. So, suppose the fan on the laptop is running faster than usual, or the temperature in the server room is fluctuating rapidly. In that case, you should check for a cryptojacking script or application.
Unexpected Loss of CPU Capacity
When you visit a website with little or no media content, you may notice a spike in CPU utilization, indicating the presence of cryptojacking scripts. Checking your device’s CPU use with the Activity Monitor or Task Manager is an excellent cryptojacking test.
However, remember that procedures may be hidden or masquerading as something legitimate to prevent you from halting the abuse. Furthermore, when your computer runs at full capacity, it will run very slowly, making troubleshooting more difficult.
Abnormal Network Traffic
Cryptojacking requires contact with mining pools or command and control servers. This requires frequent communication that is visible in network graphs. So, if you see unexplained network traffic or a substantial rise in traffic from your machine or network to a suspicious source, check for cryptojacking activities.
Browser Performance Issues
Web browsers are often used in cryptojacking attacks, and some malware are installed exclusively in the browser as extensions. So, if your browser becomes sluggish, unresponsive, or crashes frequently, it could be due to cryptojacking scripts running in the background.
Increase in Power Bills
Cryptojacking requires a significant amount of electricity, especially in a large-scale attack. If you observe an unexpected spike in your electricity bill without a change in usage patterns, cryptojacking may be to blame.
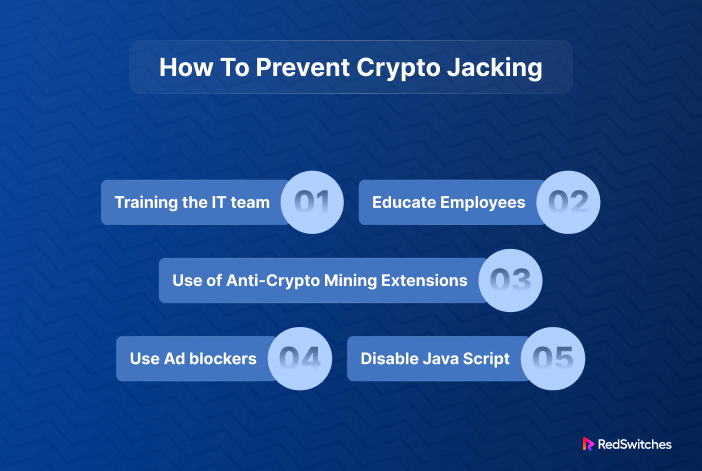
Preventive Measures
Now, let’s discuss the preventive measures you can deploy against cryptojacking:
Security Software
The first line of defense against cryptojacking is a feature-rich antimalware that detects and removes cryptojacking scripts from infected devices.
Regular Updates
Many attacks take advantage of known flaws in currently installed software. We highly recommend updating all software and device drivers with the most recent version to fix security issues. Install software only from reputable sources and avoid questionable websites that may house these dangerous scripts.
Ad-Blockers and Extensions
Cryptojacking programs are frequently placed in web advertisements. Use an ad-blocker to detect and block crypto mining code.
Monitoring and Evaluation
Real-time analysis is another critical piece of anti-cryptojacking operations. We recommend monitoring user and process activity and setting up automated risk detection alerts. In addition, keep a close eye on resource consumption to identify abnormal usage patterns.
Education and Awareness
IT teams rely on employees to notify them when machines overheat or run slowly. Employees must understand cyber security and be aware that they should avoid clicking on links in emails that may contain cryptojacking code and only download from known links.
Conclusion
In this article, we tried to answer the question: What is cryptojacking?
Cryptojacking is a growing hazard in the digital world. It involves the unauthorized use of computing resources to mine cryptocurrencies without the device owner’s knowledge or approval.
Cryptojacking can be challenging to detect due to its stealthy nature, although anomaly detection and behavioral analysis tools can assist in identifying suspicious activities. To limit the hazards connected with cryptojacking, preventive steps such as regular software updates, effective security software, and employee education are vital.
RedSwitches delivers a secure hosting environment. Our emphasis on cutting-edge security protects our clients from cryptojacking and other cyber attacks. We help protect businesses and individuals from the disruptive and damaging impacts of cryptojacking attacks by providing a secure bare metal infrastructure.
FAQs
Q: What is cryptojacking?
A: Cryptojacking is a cyber assault in which hostile actors mine cryptocurrencies on a victim’s computer, smartphone, or other connected devices without their knowledge or agreement.
Q: Can cryptojacking be used to target businesses?
Yes, corporations are frequently targeted by cryptojacking assaults because attackers regard corporate networks and servers as valuable sources of processing power. Strong cybersecurity measures and personnel education can help prevent these assaults.
Q: What are the risks associated with cryptojacking?
A: Cryptojacking can slow down devices, raise electricity bills, and potentially cause hardware damage. Furthermore, it represents a violation of privacy and security, as attackers obtain unauthorized access to personal or company devices.