Cyber security challenges affect everyone who has a device that connects to the internet.
No matter whether you’re an individual, a business, or an MNC, you can be a target for an attack because of the constant use of technology and reliance on connectivity.
While cyber security challenges/attacks are a recent phenomenon, these threats have existed since the internet’s inception.
However, despite how terrifying it may sound, you can recognize and even mitigate many security risks. This article explores the different cyber security challenges, attacks, and solutions to nullify them.
Table of Content
- What Exactly Are Cyber Security Challenges?
- Malware and Virus Infection
- Brute Force Attack
- DDoS Attacks
- SPAM and Phishing Attacks
- Data Breach
- Outdated or Unpatched System Components
- Ransomware Attacks
- Code Injection (Remote Code Execution)
- Insider Threat
- Weak Passwords
- SQL Injections
- Credential Stuffing Attack
- Trojan Horses
- Cross-Site Scripting (XSS) Attack
- Social Engineering
- Conclusion
- FAQs
So, What Exactly Are Cyber Security Challenges/Threats?
A security issue is any uncovered risk or weakness in your system that hackers could exploit to compromise systems or data.
This includes weaknesses in your company’s operations, employees, and the servers and software that connect your company to customers. All these can be potential avenues for introducing a vulnerability that can be exploited through a combination of attacks.
The best way to deal with cyber security challenges/threats is to find and fix them immediately. Remember that these vulnerabilities exist in all systems, and the only way is to discover and eliminate all the entryways and options hackers can use for their attacks.
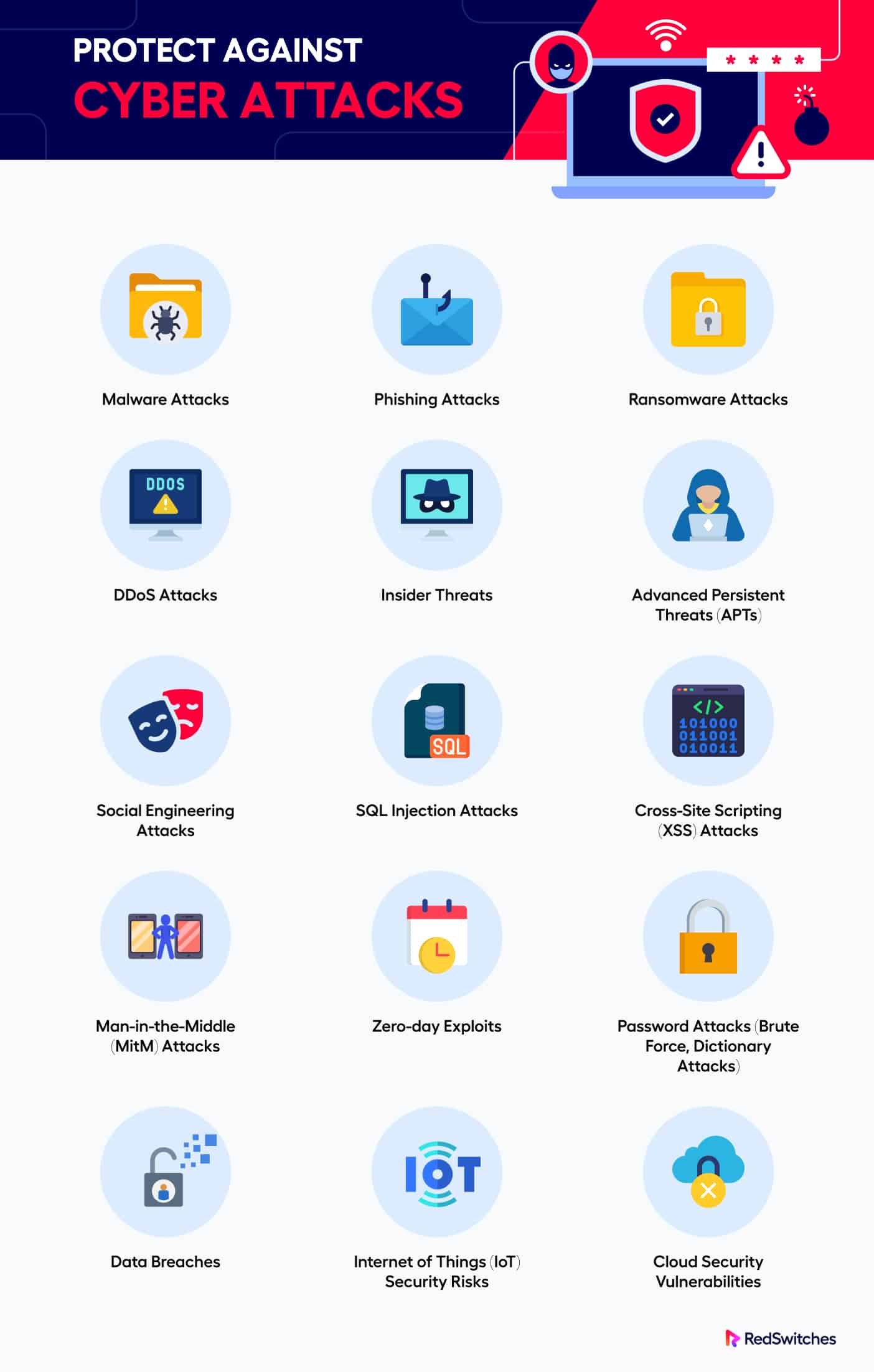
Now that you know the theoretical definition of a security threat, we’ll discuss the top 15 web cyber security challenges and the appropriate steps you can take to secure your personal information, your company’s data, and your online reputation.
But before we go into the details of the attacks, it is important to point out that security is an ongoing process. Many organizations make the mistake of deploying the best security measure and then forgetting to update or upgrade. As a result, these best-in-class security processes become outdated and transform into serious cyber security challenges to the businesses.
1. Malware and Virus Infection
Malicious software is popularly known as malware.
Malware is frequently used by hackers to gain access to your website or to use your devices to access and attack other users on the same network. For instance, malware can log keystrokes to steal passwords or even encrypt data for ransomware purposes.
If your system is infected with malware, you should know that the problem is much worse than it appears. Malware infection is usually the second stage of an attack on your systems. In the first stage, hackers usually deploy attacks that help them access your systems. Once this first stage is successful, the attackers install malware as the jump-off stage to the next attack stages.
That’s why, when fixing malware infection, you should also find and fix the ways attackers gained access to your systems in the first place.
Prevention Techniques
- Use an antivirus to scan and find the malware on a system. Keep the antivirus software up-to-date so that it can identify the latest malware on your system.
- Always provide non-administrative privileges to users and regularly review user access for specific applications/CMS.
- Regularly backing up system data to offline or remote locations is a good practice that allows your systems to return online with minimum loss of time and operational data.
2. Brute Force Attack
A brute force attack is a strategy attackers use to gain unauthorized access to a system or an account by repeatedly attempting password or encryption key combinations until the right one is discovered.
The attacker uses automated software or hosted scripts to quickly try many passwords or encryption keys in a brief period. This attack is a trial-and-error approach.
A brute force attack aims to take advantage of passwords or encryption keys that are weak or simple to guess. Common or default passwords are typically used as a starting point, and the attacker then methodically tries all other possible combinations, such as dictionary words, character variations, or incremental patterns.
Prevention Techniques
- Use strong & complicated passwords and enforce organization-wide password policies.
- Provide training to users for security awareness to avoid brute force attacks.
- Use multi-factor authentication at all levels.
- Use rate limiters that restrict or block multiple login attempts.
3. DDoS Attacks
Distributed Denial of Service (DDoS) is a coordinated attack that uses multiple compromised computers or internet-connected devices to flood a target system or network with traffic, making it inaccessible to real users.
A DDoS attack aims to consume the network bandwidth of the targeted service or website to prevent it from operating normally. DDoS attacks are frequently carried out by a botnet, a collection of compromised computers or other devices the attacker controls. Often referred to as “zombies” or “bots,” the compromised devices have malware that enables remote control by the attacker.
DDOS attacks might be over in a couple of hours, but they often result in lasting damage to the brand’s reputation, revenue loss, and service disruption.
DDOS attacks can take the following forms:
Protocol-Based Attacks: These attacks exploit flaws in the target’s application layer or network protocols to drain resources or disrupt regular communication.
Application Layer Attacks: These attacks send numerous requests that exhaust the processing capacity or database search limits to the target application or service operations.
Volume-based Attacks: These attacks involve sending a high volume of traffic that overwhelms the target system.
Prevention Techniques
- Traffic Monitoring, filtering, and Analysis help to identify DDOS attacks.
- Use scalable infrastructure to handle spikes in network traffic.
- Deploy DDOS protection measures such as IP restrictions and traffic source filters.
4. SPAM and Phishing Attacks
These are related attacks often combined to trick or manipulate users for nefarious ends.
Here’s a brief description of these attack methods.
SPAM: This is an umbrella term for all unwanted and unwelcome bulk email messages received in an inbox. These messages are frequently promotional in nature and promote goods, services, or con artists.
Phishing: In this category of attacks, hackers try to steal information like passwords, credit card numbers, or social security numbers. Phishing attacks are frequently launched through spam emails, instant messages, or websites that imitate well-known companies.
Prevention Techniques
- Users should be trained to avoid opening links or downloading files from shady or unsolicited emails.
- Users should check and verify the website’s identity before entering sensitive or personal information.
- Regularly update the operating system, software, and security tools to reduce potential vulnerabilities.
- Use email clients or solutions with strong anti-spam and anti-phishing filters to identify and block malicious messages.
5. Data Breach
A data breach is when unauthorized people or groups access private or protected information without authorization. This category of attacks includes all unauthorized acquisition, access, disclosure, or use of confidential or sensitive information by people or organizations who shouldn’t have access to it.
Data breaches can occur in various ways, like insider threats, physical theft, or cyberattacks. It may cause financial loss, personal information leaks, and damage to reputation.
Prevention Techniques
- Perform regular security checks and audits to ensure data integrity.
- The organization should place and upgrade existing security measures like robust firewalls and antivirus software.
- Proper storing and disposing of sensitive data is essential to prevent unauthorized access.
- Users should be regularly educated about the severity of these attacks and the extent of damage these attacks can potentially cause.
6. Outdated or Unpatched System Components
Unpatched systems are among the most frequently exploited systems out there. Ironically, this is the most straightforward security issue organizations can avoid.
Hackers regularly exchange software vulnerabilities to select the appropriate loopholes for their attacks. In addition, countless freely-available automated hacking tools come with sizable vulnerabilities in databases. The problem intensifies when website administrators don’t upgrade software components after installation.
Prevention Techniques
- Install and keep host-based intrusion detection systems, antivirus, and anti-malware software up to date.
- Education and user awareness about applying updates and patches.
- Plan and perform regular updates and patching.
- Keep multiple backups of the essential files and data.
- Use a patch management system/service to automate large or distributed infrastructure patching.
7. Ransomware Attacks
The most common ways ransomware spreads are through phishing websites, compromised software downloads, malicious email attachments, and exploiting security flaws in your systems.
When a device or network is infected by ransomware, all files are encrypted (often using a proprietary encryption function/algorithm).
Victims get a ransom note, which describes the situation and gives instructions on how to pay the ransom. This note is typically displayed on the victim’s screen after the encrypted files. Frequently, the ransom note threatens to permanently delete the victim’s files or raise the ransom if the money is not paid in a predetermined window.
Prevention Techniques
- Maintain frequent backups of your important files and ensure they are stored offline so they aren’t affected by ransomware.
- Use robust antivirus and anti-malware solutions and enable firewall protection.
- Regularly conduct security audits.
- Avoid downloading from suspicious sources.
8. Code Injection (Remote Code Execution)
Code injection is a class of attack that enables an attacker to insert and run malicious code inside a target application or system. In particular, attackers carry out remote code execution (RCE).
A common way of executing these attacks is when a program improperly validates or sanitizes user input, allowing unauthorized commands or code to be executed. Attackers carry out RCE by taking advantage of improperly structured applications that might contain issues like inadequate input validation, improper user input handling, or unsecured use of system functions.
During code injection attacks, hackers deploy custom-crafted inputs or payloads that deceive the application into running any arbitrary code.
Prevention Techniques
- Keep software, applications, and CMS up-to-date.
- To reduce the risk of code injection vulnerabilities, use the best security code writing techniques like input validation, output encoding, and proper security library and framework usage.
- Conduct regular code reviews to identify and address potential vulnerabilities.
9. Insider Threat
Insider threats are security risks that arise from within the organization, typically from people authorized to access internal systems, networks, or sensitive data. These people may be coworkers, vendors, or associates who act against the organization’s best interests or abuse their power. Generally, these users can be divided into the following categories:
- Insiders with compromised credentials or access rights: On occasion, outside attackers may steal insiders’ login information or access privileges.
- Negligent Insiders: Negligent insiders do not intentionally cause security incidents or breaches. However, they may unintentionally help attackers through negligence or ignorance.
- Insiders with bad intentions: These people purposefully abuse their access privileges to harm the organization.
- Malicious Insiders: These are usually disgruntled employees or industrial spies facilitating attacks from within the organization.
Prevention Techniques
- Robust access controls should be implemented, and user privileges should be reviewed and updated frequently.
- Set up reliable monitoring systems to keep records of user activity, spot suspicious behavior, and flag anomalies or out-of-pattern system access.
10. Weak Passwords
It is said that an organization is as safe as its weakest password. Organizations should always have a strict password policy that details the length and complexity of the passwords users should use for all internal and external accounts. As a rule of thumb, a good password should be at least 10 characters long, combining uppercase, lowercase, numbers, and punctuation marks.
Businesses should invest in password management solutions that keep all passwords in a vault and regularly replace passwords for critical accounts.
Prevention Techniques
- Multi-factor authentication is a strong security measure that must be enabled for every account used within business operations.
- Self-service password systems should be deployed to enforce password policies at all levels.
11. SQL Injections
SQL injections are so common that they merit a special mention in this list. In this code injection attack, an attacker “injects” malicious SQL statements in the website’s user input areas (usually forms). When processes, the SQL statements are executed on the database, damaging the data and related business operations.
These attacks happen because website developers often overlook securing the forms and validating user input. This lack of sanitation allows attackers to execute SQL injection attacks that allow unauthorized database access, data theft, and database defacements.
Prevention Techniques
- Reduce the potential impact of a successful SQL injection attack by restricting the permissions and access rights to only what is required for the application’s functionality.
- Perform security checks and testing for user input sanitation.
- To address known vulnerabilities, update the database management system and application frameworks with the most recent security patches.
12. Credential Stuffing Attack
Credential Stuffing is a cyberattack where attackers try to exploit previously used or stolen login credentials. This attack is usually manifested as a brute-force attack where hackers employ automated software to repeatedly try to log into user accounts on different websites or applications using usernames and passwords they have previously discovered in data breaches or leaks. The attack relies on the presumption that many people use the same login information for multiple online services.
Attackers can also combine dictionary attacks (usually executed through automated scripts or tools) with the credentials to improve the chances of success of these attacks.
Prevention Techniques
- Use a multi-factor authentication service.
- For each online account, users should choose a secure and distinctive password. Complex passwords should include a combination of uppercase, lowercase, numbers, and symbols. Avoid using words or phrases that are simple to guess, like birthdates.
- Implement systems to monitor and capture suspicious activities.
13. Trojan Horses
A Trojan virus, or just a Trojan, is malware that impersonates trusted software or user-generated files to trick users and gain unauthorized access to their systems.
Because it disguises itself to trick users into unknowingly inviting it inside their computers, it is named after the Trojan Horse from Greek mythology. Typically, trojans are spread via email attachments, malicious downloads, hacked websites, or file-sharing networks.
Prevention Techniques
- Install and keep your devices’ antivirus and anti-malware software updated.
- Enable firewall security.
- Follow all good practices for safe browsing.
- Keep backing up your essential files regularly.
14. Cross-Site Scripting (XSS) Attack
Hackers place malicious scripts into your web pages in Cross-site Scripting (XSS) attacks. When users arrive on these compromised web pages, they interact with the scripts and often give away personal and financial information.
These attacks become successful when web apps fail to validate or sanitize user-supplied input properly and permit the execution of unauthorized code within a user’s browser. As such, these attacks happen more because of incorrect web app and server security than user negligence.
XSS attacks can be divided into three categories that show the diverse nature of these attacks.
Reflected XSS: In this attack, the malicious script is inserted into a URL or form field, and the web application then sends the script back to the user’s browser.
Stored XSS or Persistent XSS: Here, the malicious scripts are injected into a website’s database or content management system.
DOM-based XSS: This kind of XSS attack specifically targets a web page’s Document Object Model (DOM).
Prevention Techniques
- Implement Content Security Policy (CSP) headers to define trusted content sources and limit the execution of scripts from unauthorized sources.
- Apply Incremental Security Testing to find and fix XSS vulnerabilities
- Perform regular security assessments, including vulnerability scanning and penetration testing.
15. Social Engineering
Social engineering is an umbrella term for attacks that manipulate and deceive people into accessing private information without authorization or carrying out malicious actions. Attackers use these non-technical techniques to take advantage of social interactions, psychological trigger points, and trust to achieve their ends.
Through deception or manipulation, people can be made to divulge private information, grant access to restricted systems, or take other actions that they wouldn’t usually take in a normal situation. The attackers use psychological and social principles to trick their targets and exploit their vulnerabilities.
Social engineering attacks aim to manipulate people into compromising their security by preying on human weaknesses like trust, curiosity, fear, or a desire for convenience.
Prevention Techniques
- Raise awareness about the goals of social engineering.
- Use stronger authentication processes.
- Always use independent channels to confirm the legitimacy of requests for sensitive information or actions.
- Implement strong security policies that outline best practices for handling sensitive information and will report suspicious activities.
Conclusion
As an online business, there’s nothing scarier than cyber security challenges. From data breaches to leakage of sensitive customer information, a cyber attack can impact businesses in many ways.
One of the best ways to cope with and prevent these cyber security attacks is to up your security game. Whether you’re a business owner or an employee, studying past cyber security incidents can help you determine loopholes to strengthen your security system. Moreover, choosing hosting service providers that offer optimum cyber security is ideal, such as RedSwitches.
Invest in premium bare-metal and dedicated servers with robust security measures to protect yourself from cyber attacks. With over 20+ global locations and unlimited customization options, you’re bound to get a bang for your buck.
Contact us now to learn more.
Frequently Asked Questions (FAQs)
Q-1) What is the motive behind cyber attacks?
The reasons behind cyberattacks can be different. They could be motivated by monetary gain, the theft of private information, political or ideological reasons, service disruption, retaliation, or espionage.
Q-2) How can we protect ourselves from cyber-attacks?
- Update your operating system and software with the most recent security patches.
- Use secure passwords that are different for each account.
- Be very cautious when opening email attachments or clicking any links.
- Use respected antivirus and anti-malware programs.
- When possible, enable multi-factor authentication (MFA).
- Make regular backups of your critical data.
Q-3) What should we do if we become a victim of a cyber attack?
Disconnect internet access to stop further harm or data loss. Report the incident to the proper authorities, such as your ITSec teams or a special hotline for reporting cybercrime. If your financial information has been compromised, alert your bank or other financial institutions. Change the passwords, and turn on all available security features for the affected accounts.