Digital payments are fast becoming the primary method for paying for eCommerce purchases.
As this trend gains force, the concerns about the security of these payments become critical business requirements. As a result, businesses now increasingly need to indicate their compliance with the Payment Card Industry Data Security Standard (PCI DSS), a framework designed to protect the entire payment card value chain.
While this compliance is a challenge for all businesses, small businesses, in particular, see this as a mission-critical issue because of the complexities involved in the process.
If that’s the case with you, this article will guide you through the compliance process. We’ll start with an introduction to PCI compliance and then go into the details of a PCI compliance checklist you can adopt for your businesses.
Let’s start with a short introduction to the idea of PCI compliance, and then we will discuss the PCI Compliance Checklist.
Table Of Contents
- What Is PCI Compliance?
- Scope of PCI Compliance
- The Key Pointers in PCI Compliance Checklist
- Step No 1: Install and Maintain a Firewall
- Step No 2: Remove/Modify Vendor Default Settings
- Step No 3: Set Up Protection for Cardholder Data
- Step No 4: Encrypt the Payment Data Transmission
- Step No 5: Update the Antivirus/Antimalware Software
- Step No 6: Assess and Categorize Risks
- Step No 7: Restrict the Cardholder’s Data
- Step No 8: Assign User Access Credentials
- Step No 9: Restrict Physical Access to Data
- Step No 10: Track and Monitor Network Access
- Step No 11: Ongoing Process and System Testing
- Step No 12: Create and Maintain a Comprehensive InfoSec Policy
- Conclusion
- FAQs
What Is PCI Compliance?
Businesses must comply with PCI DSS to secure credit card transactions at their checkout. The PCI compliance process covers the technical and operational guidelines to protect the credit card information given by cardholders and transferred during card processing transactions.
PCI compliance is a crucial part of the security protocol of eCommerce stores.
Scope of PCI Compliance
The process of PCI compliance covers three major areas we’ll describe below.
Identify Cardholder Data (CHD) Reception Techniques
Identify all payment channels and techniques used to gather cardholder data, from when the business receives the initial record until it is destroyed or transferred outside the business.
Identify and Monitor CHD Flows
All CHD-related processes should be documented, including the individuals, teams, and tools involved in keeping, handling, and transporting this sensitive data. This process should also document the Cardholder Data Environment (CDE) to cover all bases.
Identification of the CDE’s Accessory Components
The business should determine every system, employee, and business and technical process that can communicate with the CDE. Due to their relationship and potential impact on the security of the CHD, all of these components are referred to as “security-impacting systems” and are included in the PCI scope.
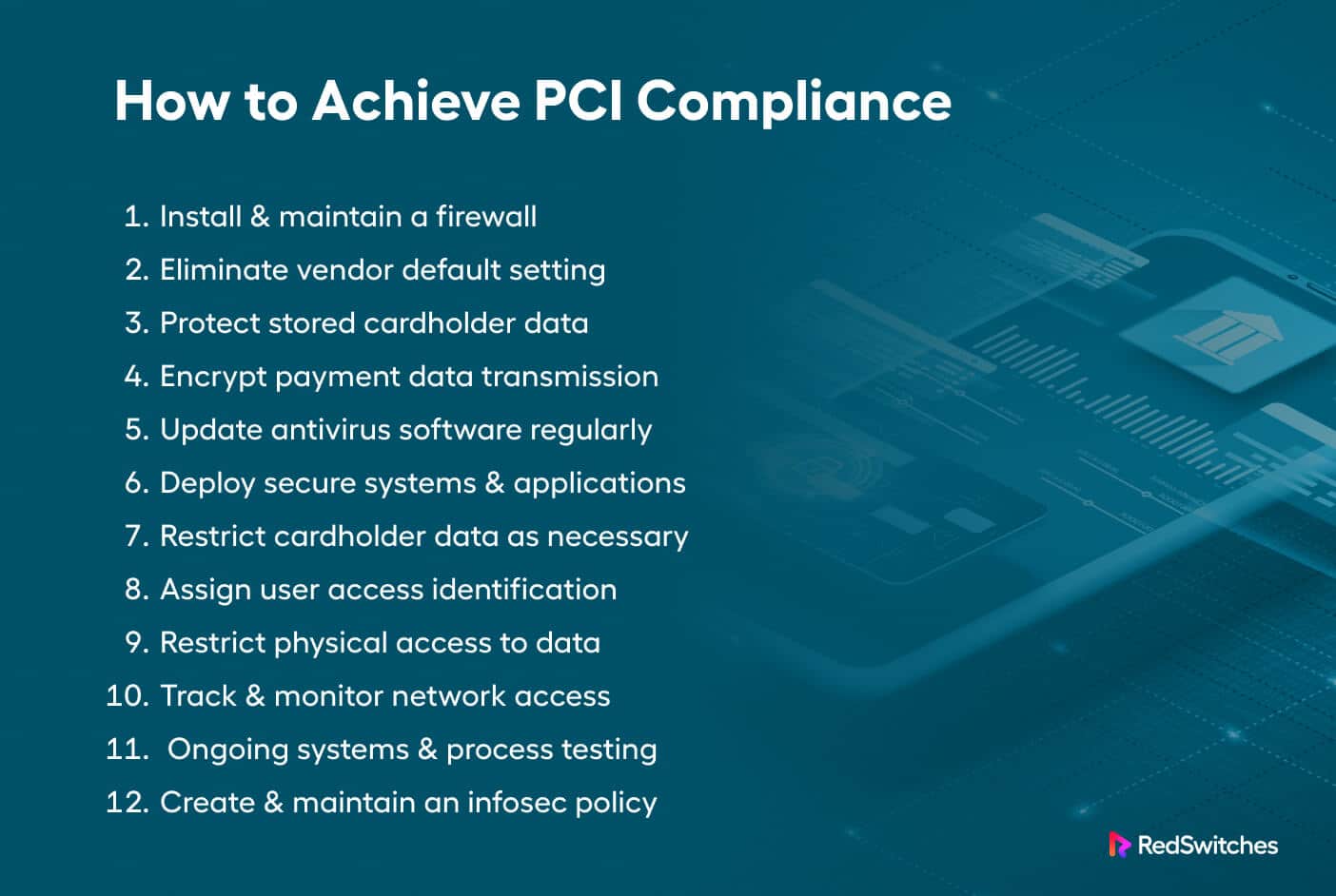
The Key Pointers in PCI Compliance Checklist
Now that you understand the scope of the PCI Compliance framework, let’s check out the significant points in a typical PCI Compliance checklist that you can adopt for your eCommerce business.
Step # 1: Install and Maintain a Firewall
The first step in achieving compliance is to satisfy the PCI DSS firewall criteria. Firewalls often serve as the first line of defense by monitoring and controlling incoming and outgoing network traffic.
You must appropriately configure your routers and firewall to safeguard the environment where credit card data is stored (CDE). The firewall rules should explicitly specify the allowed and blocked traffic sources.
Step # 2: Remove/Modify Vendor Default Settings
Never rely on the default settings of any server, network device, or software application. The default credentials and other security settings usually fall short of PCI guidelines.
According to the second PCI DSS standard requirement, you must refrain from using vendor-supplied defaults for security parameters. We recommend maintaining documentation for security hardening methods to restore these settings without any worries.
Step # 3: Set Up Protection for Cardholder Data
The most critical PCI DSS compliance requirement is protecting your cardholder data on disk. You should encrypt all cardholder data with appropriate algorithms and security keys. This is an essential step in any PCI compliance checklist and is usually accomplished by setting up a database encryption process.
Step # 4: Encrypt the Payment Data Transmission
Similar to the previous PCI DSS requirement, this step concentrates on protecting data in transit (as opposed to on-store data storage). This step covers security processes for securing CHD as it travels from the store to the next hop in the credit card processing chain.
This is a critical step because hackers often target data in transit because they perceive it is more vulnerable at this stage. Using SSL/TLS is a recommended practice for all eCommerce stores.
Step # 5: Update the Antivirus/Antimalware Software
For PCI-DSS compliance, installing security software is insufficient. You need to make sure that this software is frequently updated and patched. This PCI compliance checklist point aims to protect all your systems and cardholder data from malware and other infections.
Step # 6: Assess and Categorize Risks
The next step is to create and implement strategies for identifying and categorizing risks. In this context, the most important category is the risks associated with deploying technology to your store. A complete risk assessment is vital in managing and using technology conforming to PCI compliance requirements.
Step # 7: Restrict the Cardholder’s Data
Any PCI compliance checklist is incomplete without this step. Restricting access to CHD is a crucial requirement where access to this dataset is provided on a need-to-use basis. According to PCI DSS rules, individuals should only have access to private cardholder data when needed for business operations.
Step # 8: Assign User Access Credentials
Every user should have a unique username and password combination for accessing critical information. In practical terms, this means all users who interact with CHD should have distinctive credentials to trace access trails during a security incident. Admins should discourage or eliminate shared or group credentials. Furthermore, admins should implement industry-standard password strength rules for all users.
Step # 9: Restrict Physical Access to Data
Being PCI compliant extends beyond online security parameters. The PCI DSS standards also maintain that physical security should be taken as seriously as online security. Physical access to servers, paper files, and workstations that store or transfer cardholder data.
Step # 10: Track and Monitor Network Access
Hackers who wish to target CHD target the physical and wireless networks of the business. As a result, PCI compliance rules demand that all networks be monitored continuously, with a continuously maintained log of all activities.
This point in the PCI compliance checklist maintains that the logs should be stored on a central server for maximum security and ease of access.
Step # 11: Ongoing Process and System Testing
Cybercriminals and malicious actors continuously evolve their attack methodology to find weaknesses in your store’s defenses. The PCI standards include pointers for ongoing system and process testing so that you can ensure continuous protection of the CHD. Testing for vulnerabilities and penetration can help you identify loopholes that could let hackers in.
Step # 12: Create and Maintain a Comprehensive InfoSec Policy
The last pointer in this PCI compliance checklist is the idea of a comprehensive InfoSec
policy that covers the entire store. We highly recommend evaluating this policy to keep the store’s CHD collection and processing processes and the CDE safe.
Conclusion
Businesses that handle sensitive payment card data must follow a PCI compliance checklist. You should ensure that credit card information is collected, processed, and stored securely.
The checklist presented in this article is meant to guide businesses to adapt to their specific use cases.
Compliance with the tenets of the PCI DSS framework is a crucial business requirement, and the management should work with all stakeholders in creating and maintaining a secure environment. This is a significant step toward establishing and maintaining customer trust and business reputation.
Working with a trustworthy and knowledgeable hosting company like RedSwitches can make a big difference in complying with the PCI DSS framework requirements. Our support engineers help customers build and maintain secure infrastructure for their eCommerce business.
FAQs
1) What are the PCI compliance checklist’s main requirements?
There are usually 12 essential requirements on the PCI compliance checklist, all of which cover different security measures. These criteria include setting up strict access controls, frequently monitoring and testing systems, and ensuring the right information security policies are in place.
2) Does PCI compliance provide 100 percent protection from data breaches?
PCI compliance isn’t 100% foolproof. However, implementing a PCI compliance checklist reduces the risk of CHD leakage or theft.